
- Security Testing - Home
- Security Testing - Overview
- Security Testing - Process
- Security Testing - Malicious Software
- HTTP Protocol Basics
- HTTPS Protocol Basics
- Encoding and Decoding
- Security Testing - Cryptography
- Security Testing - Same Origin Policy
- Security Testing - Cookies
- Hacking Web Applications
- Security Testing - Injection
- Testing Broken Authentication
- Testing Cross Site Scripting
- Insecure Direct Object Reference
- Testing Security Misconfiguration
- Testing Sensitive Data Exposure
- Missing Function Level Access Control
- Cross Site Request Forgery
- Components with Vulnerabilities
- Unvalidated Redirects and Forwards
- Security Testing - Ajax Security
- Testing Security - Web Service
- Security Testing - Buffer Overflows
- Security Testing - Denial of Service
- Testing Malicious File Execution
- Security Testing - Automation Tools
Components with Vulnerabilities
This kind of threat occurs when the components such as libraries and frameworks used within the app almost always execute with full privileges. If a vulnerable component is exploited, it makes the hackers job easier to cause a serious data loss or server takeover.
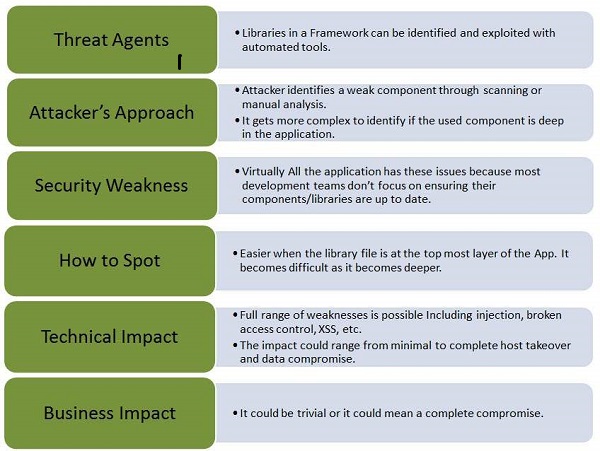
Let us understand Threat Agents, Attack Vectors, Security Weakness, Technical Impact and Business Impacts of this flaw with the help of simple diagram.
Example
The following examples are of using components with known vulnerabilities −
Attackers can invoke any web service with full permission by failing to provide an identity token.
Remote-code execution with Expression Language injection vulnerability is introduced through the Spring Framework for Java based apps.
Preventive Mechanisms
Identify all components and the versions that are being used in the webapps not just restricted to database/frameworks.
Keep all the components such as public databases, project mailing lists etc. up to date.
Add security wrappers around components that are vulnerable in nature.